Operating System Components and Services
Tom Kelliher, CS 311
Feb. 6, 2012
Announcements:
From last time:
- System architecture issues.
- I/O programming.
- Memory hierarchy.
- Hardware protection.
Outline:
- Operating system components.
- System calls.
- Operating system structure.
- Virtual machines.
Next week: kernel hacking lab.
From the virtual machine point of view (also resource management)
These components reflect the services made available by the O.S.
- User interface
- Process Management
- Process is a program in execution -- numerous processes to choose
from in a multiprogrammed system,
- Process creation/deletion (bookkeeping)
- Process suspension/resumption (scheduling, system vs. user)
- Process synchronization
- Process communication
- Deadlock handling
- Memory Management
- Maintain bookkeeping information
- Map processes to memory locations
- Allocate/deallocate memory space as requested/required
- I/O Device Management
- Disk management functions such as free space management, storage
allocation, fragmentation removal, head scheduling
- Consistent, convenient software to I/O device interface through
buffering/caching, custom drivers for each device.
- File System
Built on top of disk management
- File creation/deletion.
- Support for hierarchical file systems
- Update/retrieval operations: read, write, append, seek
- Mapping of files to secondary storage
- Protection
Controlling access to the system
- Resources -- CPU cycles, memory, files, devices
- Users -- authentication, communication
- Mechanisms, not policies
- Network Management
Often built on top of file system
- TCP/IP, IPX, IPng
- Connection/Routing strategies
- ``Circuit'' management -- circuit, message, packet switching
- Communication mechanism
- Data/Process migration
- Network Services (Distributed Computing)
Built on top of networking
- Email, messaging (Exchange)
- FTP
- gopher, www
- Distributed file systems -- NFS, AFS, LAN Manager
- Name service -- DNS, YP, NIS
- Replication -- gossip, ISIS
- Security -- kerberos
- User Interface
- Character-Oriented shell -- sh, csh, command.com (User
replaceable)
- GUI -- X, Win32
Some of the Linux system calls:
(Refer to man 2.)
- Process Management
Scheduling, deadlock detection is transparent.
- fork, vfork, exit, exec
- wait
- signals, pipes, streams, sockets
- Memory management
For the most part, transparent to the user.
- malloc, free
- I/O Device Management
Devices are treated as files, so I/O devices are supported by the file
system.
- File System
- creat, open, close
- lseek, read, write
- stat, chmod, chown
- link, unlink
- mkdir, rmdir
- sync
- Communication
Two models:
- Message passing
- Processes communicate by passing messages -- mailbox model.
- Primitives: send, receive.
- Each Process has a private address space.
- Perfect for inter-processor communication. No synchronization
problems. Latency can be a problem. Queueing.
- Shared memory
- Processes communicate by sharing memory -- bulletin board
model.
- Primitives are implicit once spaces are mapped.
- Good for large amounts of intra-processor communication.
Synchronization problems.
Issues: naming, security, transparency, replication, etc.
Message passing
- socket, bind, accept, read.
- socket, connect, write.
Shared memory:
- mmap.
Definitions:
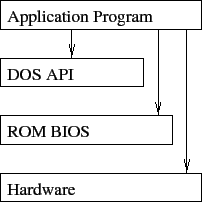
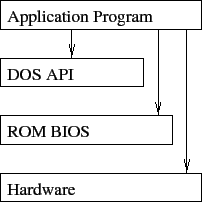
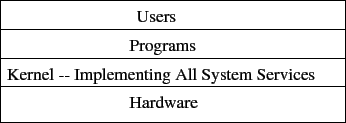
- Layered System -- A system in which pieces are built on top of other
pieces, with hardware as a foundation. A layer make calls
exclusively to the layer beneath it.
Advantages:
- Well defined structure.
- Modular.
- Information Hiding.
Disadvantages:
- Poor performance on ``deep'' calls -- latency.
- Difficulty in creating a ``good'' layered design.
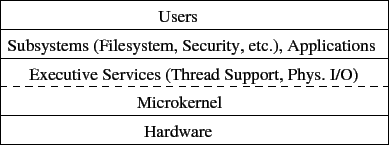
- Micro Kernel -- A small executive that provides only necessary
functionality to support threads/processes:
- CPU scheduling.
- Process primitives: create, destroy, suspend, activate, change
priority, etc.
- IPC.
- Virtual Memory.
- Interrupt handlers.
- Device driver interface.
Runs in kernel (supervisor) mode. Everything else runs in user mode.
Advantages:
- Only a small amount of code runs in kernel mode.
- Easily extended.
- System routines work with an abstract machine model -- portability.
Disadvantages:
- System calls require a context switch (slow).
- Not easily extended (traditional kernel).
Weak layering:
Traditional kernel:
Micro kernel:
Lowest software level (between kernel and hardware) provides a virtual
machine interface to multiple, independent kernels. VMware. Java
VM.
- Support for OS development alongside a production system.
- Virtual user/kernel mode, real user/kernel mode.
- How is a disk operation carried out?
- Virtual Machine is/isn't a simulation/emulation:
- Java VM: simulate one architecture with another.
VMware, Xen, MS Virtual Server, not so much.
- Efficiency?
- How are physical devices (a disk) ``virtualized?''
- Java portability: ``Write once run anywhere.''
- Java security: the ``sandbox.'' Access to local resources. Security
or impediment to application development?
- Java consistency: same look, feel between platforms?
Thomas P. Kelliher
2012-02-04
Tom Kelliher